How to Identify the Basic Signs of Insider Threats to your Local Network
Insider threats are cyber security breaches that stem from a trusted employee or vendor allowing an outsider to gain access to the local network. It’s a frustrating and difficult cyber…
Chrome and Firefox Exploits using CSS and HTML5
Insider threats come in all different shapes and sizes. Many times it’s not malicious in any way even though they come directly from your own employees. A recent vulnerability found…
Routers Under Attack from Russian Hackers through Default Passwords
One common element of all networks is the existence of routers. These devices weren’t always used in household networks. But they soon became commonplace with any home network. Because they…
Attackers Still use Drupalgeddon2 Vulnerabilities for Cryptojacking
A vulnerability in Drupal’s content management system was found weeks ago. But as with many patches site owners either don’t know that they need to patch their software or they…
€20,000,000 or 4%? – GDPR
You knew it was coming, and while initially, you may have been in denial, you can’t ignore it anymore. The General Data Protection Regulation (GDPR) is going into effect on…
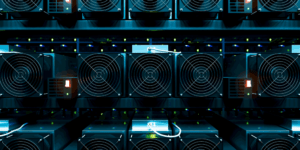
Insider Threats and the Dangers of Crypto Mining to the Enterprise
Although there has been several debates on the advantages and disadvantages of cryptocurrency and the enterprise, one issue with it is cyber security. Dealing with bitcoin or any other cryptocurrency…
When Human Error Sends Panic Across the Country
On January 13th, the state of Hawaii went into a state of panic when they received an emergency text message telling them that a ballistic missile was incoming. It took…