HIPAA / HITECH COMPLIANCE
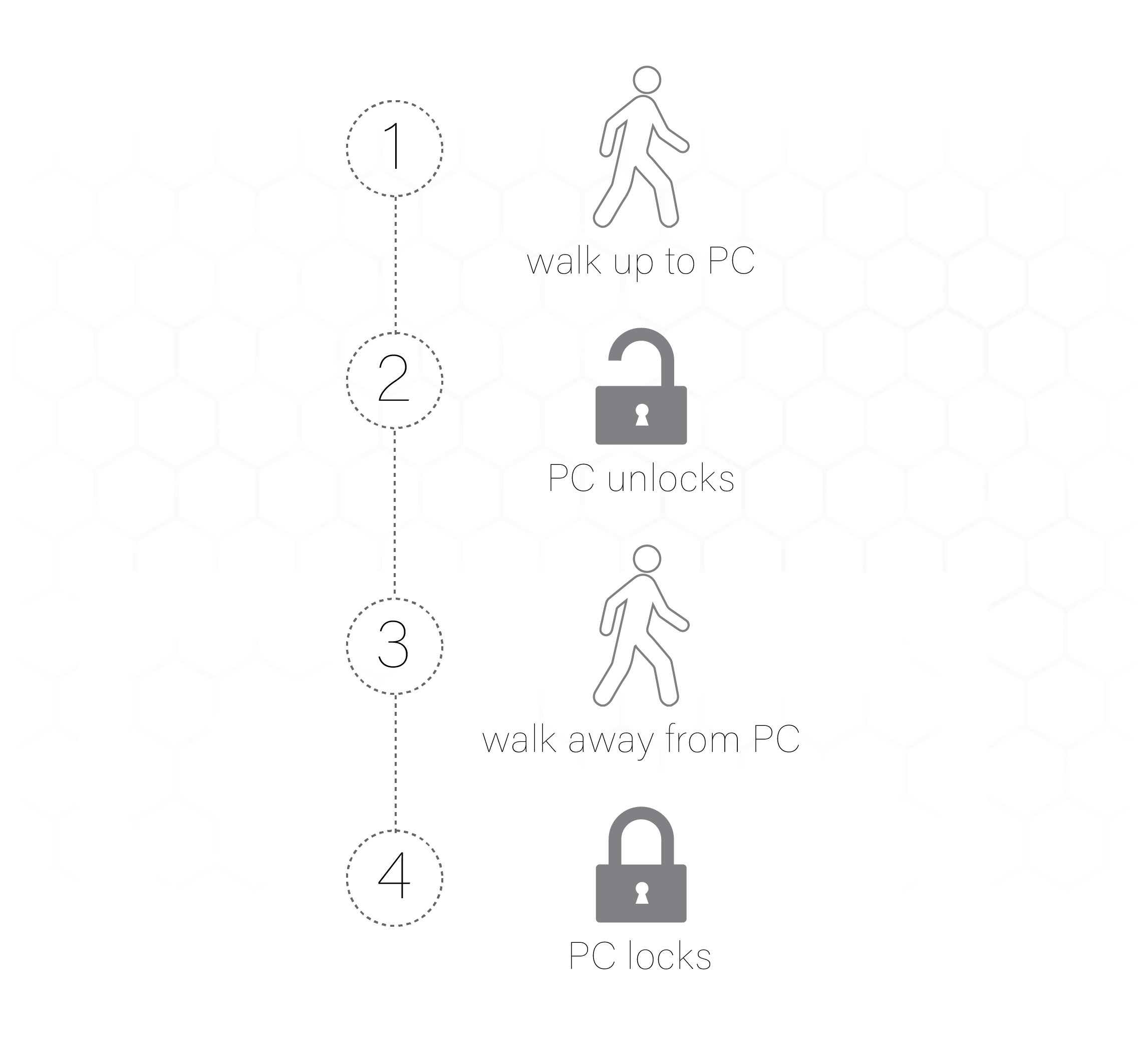
Auto-Lock unattended workstations.
Meet HIPAA compliance mandates without using passwords. No more worrying about unlocked workstations. Even with shared accounts, know which user accessed which computer when. Token-based proximity authentication means auto-enforcement of password and access security policies.
HIPAA Security Rule compliance made easy. Ensure only permissible users access information. GateKeeper helps healthcare clinics effectively protect PHI without effort.
"The latest versions of their tools are very impressive. I use their Halberd on my desktop just so I don’t have to always enter my long password. It is important to note that these tools still have 2 factors that are used to log into accounts. You must have the device and a password. I still see folks in hospitals grumble and enter a password from time to time."
Help Me With HIPAA
"We no longer need to remember to lock our workstations nor keep track of complex passwords!
I believe in GateKeeper, and I believe in the Untethered Labs team. They are going places, and I am glad to be on the ride with them!"
Dr. Toyin Opesanmi, M.D., AAHIVS
Gennesaret Medical Center

“A big part of keeping the patient information safe and secure is locking your computer when you have to leave the room. As we are working in the mouths of our patients, you can imagine that pressing the keys on your keyboard is not very sanitary and you have to decontaminate everything you touch before your next patient.
Thanks to the GateKeeper Enterprise system, we lock our computer automatically when we (with our Halberd or phone) are out of range of the computer. Without the key, you need to type in a password or a PIN code to unlock the computer, so this ensures that the information is kept secret and safe from prying eyes.“
Paul van Straten, Co-Owner
ESTL Tandprothetiek

"Untethered Labs’ GateKeeper Enterprise product delivers greater computer security built around the realities of our busy workplaces and workflows by using two-factor authorization and authorized proximity detection to enable access to network applications. Moving away from a user’s workstation shuts down access to prevent unauthorized access. Data breaches make the news, so providing central password control and comprehensive auditing capabilities are essential to protecting your customers, while improving their security footing."
Paul Boucherle
Security Sales & Integration
“The #1 Technology & Business Authority Since 1979”

”...an inexpensive and hassle-free way to ensure you can sit down and get to work without delay but securely lock your machine—with no user interaction—whenever you need to step away.”
David Cieslak, CPA/CITP
Journal of Accountancy
GateKeeper Enterprise HIPAA Compliance Summary
Security mechanism that increases security and decreases complexity of access. The U.S. Health Insurance Portability and Accountability Act requires safeguards against unauthorized users and information breach. Non-compliance by employees pose the greatest security risks. See how GateKeeper helps you adhere to HIPAA compliance by taking the burden off both users and admins.
| Section | Key Activity | Performance Criteria | GateKeeper Solution |
|---|---|---|---|
| 164.306(b) | Flexibility of Approach | (1) Covered entities and business associates may use any security measures that allow the covered entity or business associate to reasonably and appropriately implement the standards and implementation specifications as specified in this subpart. (2) In deciding which security measures to use, a covered entity or business associate must take into account the following factors: (i) The size, complexity, and capabilities of the covered entity or business associate. (ii) The covered entity's or the business associate's technical infrastructure, hardware, and software security capabilities. (iii) The costs of security measures. (iv) The probability and criticality of potential risks to electronic protected health information. | GateKeeper increases the security and decreases the access complexity of the covered entity by providing an automatic mechanism for the locking of a workstation when a user is no longer in proximity. A user does not have to manually lock their workstation when they are no longer present. This security mechanism decreases the potential risks to ePHI. |
| 164.308(a)(5)(ii)(C) | Security Awareness, Training, and Tools -- Log-in Monitoring | Procedures for monitoring log-in attempts and reporting discrepancies. | GateKeeper Enterprise provides auditing and monitoring of all login events. |
| 164.310(c) | Workstation Security | Implement physical safeguards for all workstations that access electronic protected health information, to restrict access to authorized users. | GateKeeper provides a mechanism to automatically prevent unauthorized access to unattended computers. |
| 164.312(a)(2)(i) | Access Control -- Unique User Identification | Assign a unique name and/or number for identifying and tracking user identity. | Each GateKeeper token (key) address is associated with a user identity. Users can be identified and tracked by the hardware/software token identifier. |
| 164.312(a)(2)(iii) | Access Control -- Automatic Logoff | Implement electronic procedures that terminate an electronic session after a predetermined time of inactivity. | Combined with an organization’s group policy for automatic logoff, GateKeeper provides an additional layer of access control by automatically locking a workstation when a user is no longer in proximity. Unlike timeout policies, GateKeeper reacts instantly to a user leaving their terminal. |
| 164.312(b) | Audit Controls | Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use electronic protected health information. | GateKeeper audits user login activity within the enterprise platform at all times. |
| 164.312(d) | Person or Entity Authentication | Implement procedures to verify that a person or entity seeking access to electronic protected health information is the one claimed. | GateKeeper's secure identity and access management solution uses a hardware or software token associated with an active directory account to create a strong multi-factor authentication system. |
Automatically know who accessed what PC and when to stay compliant without effort.
Finally, see GateKeeper Enterprise advanced MFA in action.
Take a self-guided tour of how you can evolve from passwords. Then you're really saving time with automation.
Enterprise 2FA with tap and go login plus an integrated password manager. One key for all your passwords. Experience fully automated login and security. For example, faster MFA, auto-OTP, password manager, and worry-free workflow with proximity-based privileged access management for Windows 11, 10, 8, 7, VPNs, websites, and desktop applications including MES, EHR, CAD/RMS, and more. Overall, a massive upgrade to security and efficiency.




