Insider Threats and the Dangers of Crypto Mining to the Enterprise
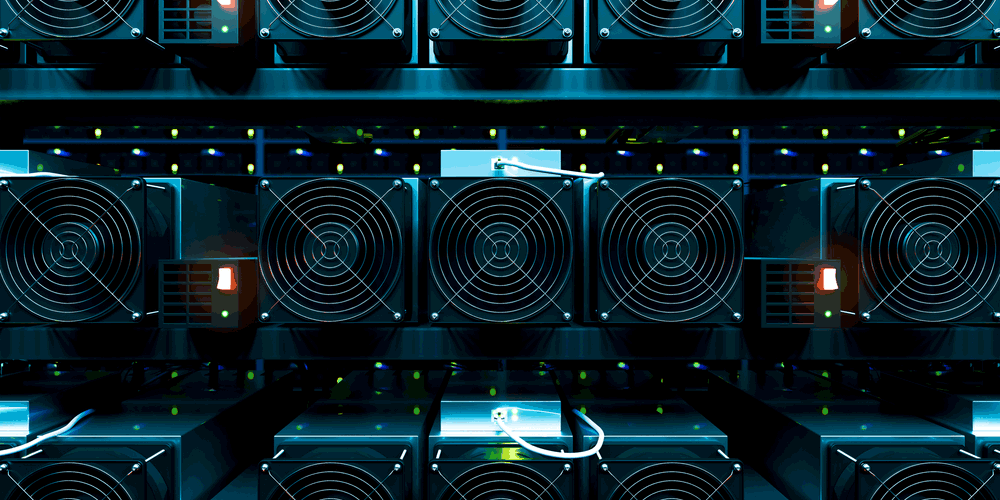
Although there has been several debates on the advantages and disadvantages of cryptocurrency and the enterprise, one issue with it is cyber security. Dealing with bitcoin or any other cryptocurrency could be an advantage for revenue. But cyber security experts are concerned with the risk of mining and using internal resources on the local network. In addition to insider threats, hackers have turned to embedded malware on malicious websites to steal resources from a viewer’s computer and use them to mine cryptocurrency through a crypto mining malware software.
Crypto Currency Mining Malware
With the boom in Bitcoin prices, mining cryptocurrency has been a way for end users to build wealth. It’s unregulated and volatile, but early miners have made millions after the increased price in bitcoin. Many of them have moved their investments into other cryptocurrency such as Ethereum, Litecoin, or Monero.
The type of coin a user mines doesn’t matter, but the resources needed to mine crypto put a strain on the local network. Mining cryptocurrency takes more electricity than usual, so you might see utility costs increase when users are mining cryptocurrency on the network. This is because mining requires user machines to use CPU and memory resources to perform calculations. Each time the machine successfully performs a calculation, a crypto is produced. The amount of money the user makes depends on the cryptocurrency mined and the value of that cryptocurrency. Crypto mining malware is on the rise.
The change in electricity usage is astronomical. So don’t disregard the changes in what you could see as a very high utilities bill. For the average gamer, playing 8 hours of games consumes about 2,000 kW/h per year of electricity. With mining cryptocurrency, the same person using a computer for 8 hours a day could use up to 5,000 kW/h each year. These figures only reflect one computer in use. But many users will add several systems to their mining operation. If an insider has access to servers or more powerful machines on the network, this would be primary targets. But would greatly increase utility costs and slow network productivity.
Hackers and Crypto Exchanges
Another issue with cryptocurrency in the enterprise is the exchanges where users buy and sell on the market. These exchanges are built by developers that don’t always think like an attacker, and they’ve been hacked to steal money and private data from end users. Some attacks have destroyed the exchange and caused it to fold. Other attacks are from the exchange owner such as Dogecoin where money was withdrawn and one person runs off with all of the crypto money.
For the enterprises, having users work with exchanges while on the network could be the loss of data or worse. Cryptocurrency miners with malicious sites normally just work with code that steals computer resources, but exchange hackers are targeting theft of coin and real money. Read about more data breach incidents.
Defending Corporate Networks from Cryptocurrency Mining
The first step is to create a policy around mining and why it’s a violation to use work computers for mining cryptocurrency. Some antivirus software has become better equipped to identify mining hacks on malicious pages. But these applications are still not to a good point where they fully defend against all of the attacks in the wild.
Filtering sites that are known to contain malware is another option. Some companies rely on a myriad of filters and flagged sites to avoid having users browse them. These work well too and can stop the problem before users are able to see spikes in computer resource usage. IT admins must actively monitor for all kinds of threats.
For more information about insider threats and what you can do to defend your network, check out GateKeeper Proximity. Prevent hackers from installing crypto mining malware. Hackers know it’s worth it.
Finally, see GateKeeper Enterprise advanced MFA in action.
Take a self-guided tour of how you can evolve from passwords. Then you're really saving time with automation.




