A Recent Ticketfly Data Breach Reminds Consumers to Use Incomplete Data When Possible
Data breaches obviously leak private information to nefarious people. They then sell it on the black market or use it for financial gain. But how do consumers know when a…
Attackers Still use Drupalgeddon2 Vulnerabilities for Cryptojacking
A vulnerability in Drupal’s content management system was found weeks ago. But as with many patches site owners either don’t know that they need to patch their software or they…
€20,000,000 or 4%? – GDPR
You knew it was coming, and while initially, you may have been in denial, you can’t ignore it anymore. The General Data Protection Regulation (GDPR) is going into effect on…
More Malicious Sites Threaten Your Organization’s Cyber Security
Having Internet access is a must for most employees. They need it for various productivity tasks. What was once a “nice to have” is not necessary for job function. IT…
Malware Writers Use Memcached Servers to Amplify DDoS Attacks
Insider threats aren’t just malicious attacks on your network. Poorly configured servers present more risks. Whether it’s negligent IT configurations or improperly updated critical software, these threats can do massive…
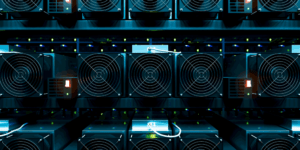
Insider Threats and the Dangers of Crypto Mining to the Enterprise
Although there has been several debates on the advantages and disadvantages of cryptocurrency and the enterprise, one issue with it is cyber security. Dealing with bitcoin or any other cryptocurrency…
When Human Error Sends Panic Across the Country
On January 13th, the state of Hawaii went into a state of panic when they received an emergency text message telling them that a ballistic missile was incoming. It took…
The First Line of Defense in Cyber Security
Headlines continue to provide us with more information on large data breaches like Yahoo and Equifax, where cyber attackers gained access to personal information through gaps in security software. But…
How do Cryptocurrency Hardware Wallets Work?
How Does a Cryptocurrency Hardware Wallet Work? The cryptocurrency market continues to grow with many new technological and innovative advancements. The hardware wallet is such an advancement – it stores…