
Benefits of Hardware Tokens for Authentication
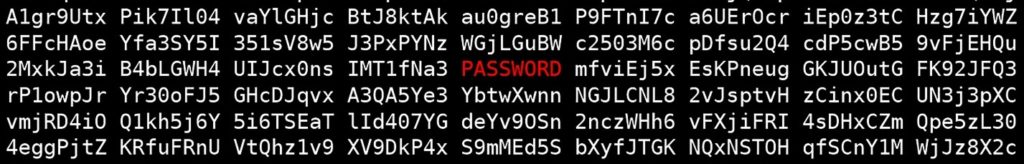
IT administrators have many responsibilities that require elevated access to the systems that they are responsible for maintaining. This makes them attractive targets for attackers looking to penetrate the most sensitive systems that they control. It’s a well-known fact that many companies are still not taking appropriate measures to protect their privileged access. To complicate the problem, there are enterprises that do not enable additional security for their administrator accounts. The Verizon Data Breach Report points out that the top observed malware in 2020 was password dumping, which focuses on extracting credentials that can be reused at a later time.
Stronger Security using Hardware Tokens
Any attempt to reduce your attack surface must involve building additional security controls around privileged access. The National Institute of Standards and Technology recommends implementing multifactor tokens as an additional layer of security, particularly for senior executives and system administrators. This reduces the chance that attackers who got access to legitimate credentials can reuse them and successfully impersonate privileged users. Multifactor controls are highly effective as demonstrated by Microsoft. Their studies show that 99% of automated passwords attacks were stopped by implementing multifactor authentication.
A simple and highly effective solution to implement these defenses and enhance security involves proximity tokens for multifactor authentication. User need two authentication elements to login successfully: something you know (password) and something you have (hardware token). Grant access only when both elements are present. If an attacker steals an administrator’s credentials, they will be unable to gain access to your systems without the token being present. Users can leave their workstations with their token and the computer will lock automatically. This additional layer of security provides peace of mind and further reduces the chances of a compromise.
Google and several universities performed a study comparing account takeover prevention rates between different methods. The study showed that only users that used security tokens for 2FA had a 100% prevention rate against multiple account takeover methods including automated bots, bulk phishing attacks, and targeted attacks. Localized hardware token-based 2FA also minimizes the attack vector to physically in front of the computer. This is where protected buildings, gates, locked doors, and physical access control also contribute to the overall cybersecurity posture.
Easier to Manage Users = Fewer Mistakes
Provisioning and deprovisioning passwords are also simplified by using hardware tokens. For use cases where an administrator needs to share passwords with a user, a few simple steps in the administration portal can help accomplish this.
When employees depart, instead of trying to figure out every single account that a user has access to, proximity tokens can help automate the workflow necessary to reset or deprovision multiple account passwords. This allows to reduce administrative burden associated with employee turnover, reduce errors, and save time.

Adoption of proximity tokens can enhance the security of your platforms by simplifying authentication (2FA/MFA) beyond what other methods can achieve. Flexibility for administrators and users make it a perfect addition to a well-thought security defense in depth strategy. Another advantage of hardware-based authentication is that stronger continuous authentication is also possible.
Finally, see GateKeeper Enterprise advanced MFA in action.
Take a self-guided tour of how you can evolve from passwords. Then you're really saving time with automation.




