Hospital Cyber Risks of Computers in High-Traffic Areas
The Silent Threat: Cybersecurity Risks of Computers in High-Traffic Public Areas like Hospitals
Introduction
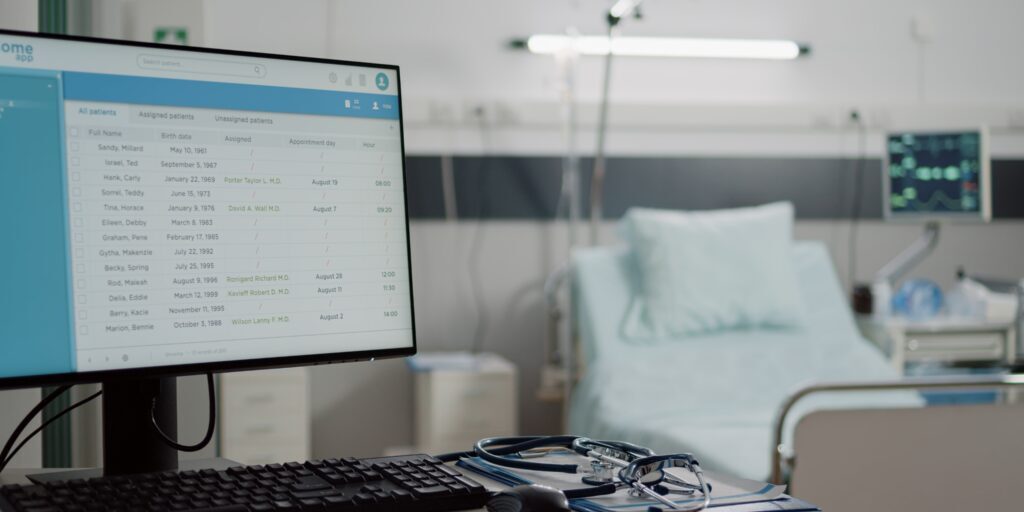
As organizations strive for efficiency and ease of use, they increasingly deploy computer systems in public and high-traffic areas. Hospitals are no exception, featuring computers at nursing stations, reception desks, and patient rooms. While these placements serve operational needs, they pose severe cybersecurity risks that are often overlooked. This article aims to discuss the potential risks and ramifications of unsecure computer and password policies in such areas, fortified with compelling real-world examples and data.
The Risks
Unlocked Screens
- Unauthorized Data Access: An unlocked screen can act as an open window into the confidential data of an organization. Anyone can view sensitive patient records, financial information, and other confidential data.
- Data Manipulation: The risk extends beyond mere viewing. An unauthorized person could alter critical data, jeopardizing patient care and institutional integrity.
Weak Password Policies
- Brute Force Attacks: There’s a chance that weak passwords can be guessed or intercepted in areas where passcodes are input frequently.
- Password Reuse: Staff may resort to using the same passwords across multiple systems, making it easier for attackers to gain unauthorized access to multiple platforms.
Real-World Examples
- Stolen Patient Data: In 2018, a hospital in California reported that an unauthorized individual accessed a computer at a nursing station, compromising the data of 528 patients.
- Financial Fraud: A large healthcare provider in New York suffered a cyber incident where an open computer in a public area was used to divert $1.2 million to an offshore account.
The Data
- A Ponemon Institute study revealed that 56% of healthcare organizations have been negatively impacted by a careless employee or contractor who compromised data.
- IBM’s Cost of a Data Breach Report (2021) shows that the average total cost of a data breach in healthcare is $9.23 million, far exceeding the average of $4.24 million across all industries.
Ramifications
Legal Consequences
- Non-compliance with regulations like HIPAA can lead to heavy fines and legal actions.
Financial Losses
- The cost of resolving a breach, legal consequences, and reputational damage can cripple an organization.
Erosion of Trust
- Patients are less likely to trust a hospital that can’t properly secure their data, let alone their health.
Solutions
- Automated Screen Locks: Implement policies that require screens to lock automatically after a brief period of inactivity.
- Two-Factor Authentication: This adds an extra layer of security, making it difficult for unauthorized users to gain access.
- Regular Staff Training: Conduct regular cybersecurity training to ensure all employees are aware of best practices.
- Continuous Monitoring: Use advanced analytics and machine learning algorithms to monitor for unauthorized access.
Conclusion
Computers in high-traffic areas such as hospitals are not just operational assets but also potential liabilities if not appropriately secured. Organizations must act urgently to mitigate these risks, employing robust cybersecurity measures to protect sensitive data and systems. Failure to do so puts not just data, but human lives and institutional integrity, at significant risk.
With staggering financial implications and severe repercussions for patient care, cybersecurity is not an optional extra but an essential component of modern healthcare. This is a call to action: let us secure our systems as vigilantly as we guard our patients’ well-being.
For an in-depth consultation on how to improve your organization’s cybersecurity posture, feel free to reach out to our team of experts at GateKeeper Enterprise. Or check out other reviews by customers.
Finally, see GateKeeper Enterprise advanced MFA in action.
Take a self-guided tour of how you can evolve from passwords. Then you're really saving time with automation.




