How the ENIGMA Cipher was Hacked in World War 2

The Insider Threat that Compromised the ENIGMA Machine
Brute-Forcing the ENIGMA Cipher with Automation
Codebreakers were racing to decrypt thousands of messages a day. It quickly became apparent that for such tasks to be ultimately successful, some form of automation would have to come into play. The scale of the challenge was simply too much for manual calculations by humans. They needed speed to break the messages faster.
At some point, the Rajewski knew how the ENIGMA machine worked and could reverse-engineer it. But that still doesn’t mean you could just read messages. The problem is that the ENIGMA had too many different key setting combinations. Also, the Germans changed the settings often so finally decrypted messages came too late to be of use.
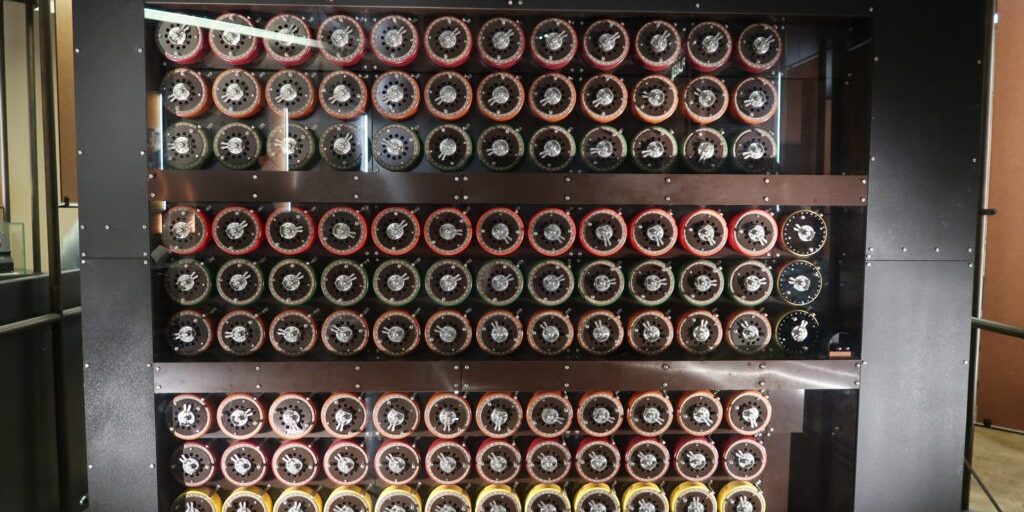
Now comes the computing power needed to try to decrypt a message against as many combinations as possible – brute-forcing the issue. It’s like if the hacker knew how a password-username system worked, all they need to do is try as many password combinations as possible. Obviously, the Germans weren’t going to make it easy. So, Rajewski’s team built an electromechanical machine (basically a quantum computer for the times) to automate the combination-trying process. They said the machine could do the work of 100 people. This machine was called a “bomba”.
Human Error will Always Mess Things Up
Allied codebreakers were trying to crack the ENIGMA cipher, but they were missing a few pieces of the puzzle. One of the vital clues that led the Allies being able to finally decrypt ENIGMA code was human error German’s part. Every message ended with the phrase “Heil Hitler”, which gave the Allies a baseline to infer how the cipher worked.
Even before that, Rajewski was able to use German communications (human) error to determine how to break the ENIGMA cipher. People are indeed the weakest link.
Finally, see GateKeeper Enterprise advanced MFA in action.
Take a self-guided tour of how you can evolve from passwords. Then you're really saving time with automation.




