Password Security Rules: Choose Length Not Complexity
You’ve been snoozing that annoying security popup for two weeks and time has run out. Password rules are being broken too often and brazenly.
Your password needs updating.
Even as an administrator you find this annoying. Imagine how the rest of your organization feels—and they probably don’t care about security as much as you do.
When was the last time you saw this during a password refresh?
Your password has failed to meet the criteria:
- Must be at least 8 characters long and contain:
- At least one uppercase letter [A-Z]
- Two lowercase letters [a-z]
- One numeral [0-9]
- One special character, but not [! or ?]
- Can’t contain your login ID, email address, or name
- No repeating character strings of 3 or more identical characters (E.g. ‘’333” or “xxx”)
- You must also make a sound while clapping with one hand
What the?!?
Of course, we’re joking at the last password requirement, but the truth isn’t all that far off. The criteria seem to be a moving target, and just when you think you’ve got it figured out, the requirements change again. Keep up with the latest best practices in password and computer security.
But strong passwords are necessary, aren’t they?
Today, passwords must be more complex, and for good reason. If a determined hacker wants to run a brute-force attack on your website to steal a password, it’s easier especially if it’s shorter. Do you remember the 2014 iCloud security breach where celebrity photos were stolen from their iCloud accounts? A brute-force attack was responsible for this. The good and bad news is that it could have been prevented if password requirements were more complex AND longer. Prevent brute-force attacks by using long, complex passwords and 2FA.
Longer is better when it comes to cracking the password code.
This might come as a shock, but a straightforward and long password is more difficult to crack than a complicated, but short password.
But here’s the thing: It turns out that the “strong” password requirements we’ve all come to know aren’t really helping. In fact, they may be doing more harm than good.
The frequency of password changes could be a big waste of your time.
Password change policies that have users switching up their passwords is a questionable practice because it may not actually increase Internet security.
The FTC’s chief technologist, Lorrie Cranor, tends to agree, “Frequent password changes do little to improve security and very possibly make security worse by encouraging the use of passwords that are more susceptible to cracking.” She’s also a professor at the School of Computer Science and the Engineering and Public Policy Department at Carnegie Mellon University and is the director of the Carnegie Mellon Usable Privacy and Security Laboratory.
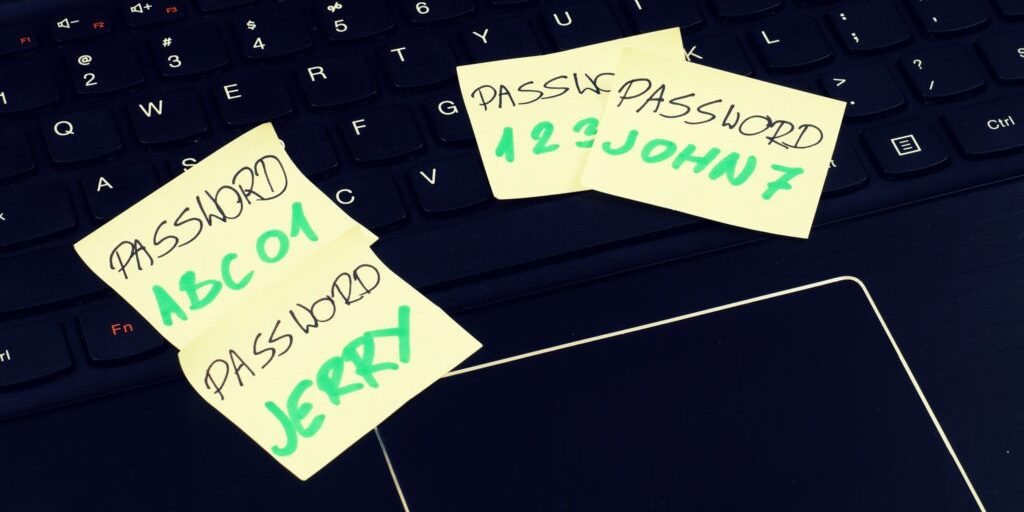
When considering how often your organization should enforce password changes, consider the bigger picture, which includes the human element. When your company enforces complex passwords that need to be changed once every 30 or 60 days, you’re asking for employees to start using some lazy practices that could leave your data vulnerable. Looking at you Password123. Stop using weak passwords! Prevent compromised situations to reduce the need to change passwords so often.

Do this instead:
There’s no one-size-fits-all answer to the best password rules, however, here are some smart suggestions to consider the next time you revisit your Internet security policy:
- Check your password and see how secure yours is with this password security checker.
- Change your passwords after a breach. If you think your password was compromised or you’ve had an electronic device stolen, change your password ASAP.
- Consider making it even longer. Mark Burnett, author of the book, Perfect Passwords agrees, “A longer password is usually better than a more random password,” he states, “as long as the password is at least 12-15 characters long.” The folks at NIST want to make passwords even longer and advises service providers to allow passwords up to 64-characters long.
- Consider removing mandatory time expiration for passwords. Or at the very least, extending the time period. With a secure password, changing it every 30, 60, or even 180 days could be unnecessary. Consider only requiring password updates every 6 to 12 months.
- Keep it quirky. The weirder, the better. Think about stringing four random words together; wood+dingo+horse+jupiter. Make it hard to guess for hackers.
- Use a different password everywhere. Once you’ve crafted the most genius of passwords, you might be tempted to use it everywhere. This is a bad idea, because if just one organization has a breach, that super awesome password you were so proud of, is also in several other spots. Use a different password for every login. A password manager tool such as Dashlane or LastPass can make this easier. Do not reuse passwords or let any of your employees either.
- Add another layer of security. Adding multi-factor authentication could be your company’s safest bet to use in partnership with a password, particularly if your organization stores sensitive data.
Better Password Rules and Practices
If you’re not already thinking about password practices, today has never been better to start seriously considering how you’re protecting your organization’s data. It’s time to pivot away from passwords that are usually only using a single word with perhaps a few numbers tacked into the end and begin using longer passphrases which could be a sentence or multiple words strung together. This not only adds more protection from a brute-force attack, but they can also be easier to remember. Which is easier to recall? K4abD&3m! or I-like-drinking-craft-beer-every-day?
Before your next password policy refresh, first, consider the costs and benefits of mandatory password changes and consider making other changes to your password policies or adding an extra layer of security rather than forcing all users to keep changing their already simple passwords. Enforce strong passwords and 2FA for all employees. Your employees will thank you for giving them one less thing to worry about. Enforce passwords rules without burdening the end users.
Finally, see GateKeeper Enterprise advanced MFA in action.
Take a self-guided tour of how you can evolve from passwords. Then you're really saving time with automation.




