Phishing and Email Fraud are Top Security Risks for Corporations
Email is essential for business, but it’s also a top concern for security administrators that need to protect the internal network from data breaches and loss of digital assets. With…
Healthcare Organizations are Among the Biggest Targets for Attackers
Of all the organizations threatened by insider threats, healthcare companies top the list. In the past several years, healthcare organization data is among the top of the list in the…
How to Identify the Basic Signs of Insider Threats to your Local Network
Insider threats are cyber security breaches that stem from a trusted employee or vendor allowing an outsider to gain access to the local network. It’s a frustrating and difficult cyber…
€20,000,000 or 4%? – GDPR
You knew it was coming, and while initially, you may have been in denial, you can’t ignore it anymore. The General Data Protection Regulation (GDPR) is going into effect on…
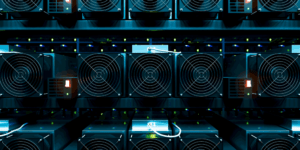
Insider Threats and the Dangers of Crypto Mining to the Enterprise
Although there has been several debates on the advantages and disadvantages of cryptocurrency and the enterprise, one issue with it is cyber security. Dealing with bitcoin or any other cryptocurrency…
The First Line of Defense in Cyber Security
Headlines continue to provide us with more information on large data breaches like Yahoo and Equifax, where cyber attackers gained access to personal information through gaps in security software. But…
GateKeeper Assistive Technology for Logging In
The best office tech helps you get your work done with efficiency and convenience. But when you’re working with a disability, challenges to that kind of unthinking ease can crop…
Medical Cyber Security with GateKeeper
Medical cyber security automated for doctors and nurses. GateKeeper is a localized wireless tracking solution that allows for constant real-time monitoring of personnel in a pre-determined and well-defined location. Personnel…