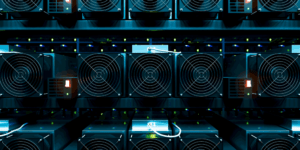
Insider Threats and the Dangers of Crypto Mining to the Enterprise
Although there has been several debates on the advantages and disadvantages of cryptocurrency and the enterprise, one issue with it is cyber security. Dealing with bitcoin or any other cryptocurrency…
Read MoreWhen Human Error Sends Panic Across the Country
On January 13th, the state of Hawaii went into a state of panic when they received an emergency text message telling them that a ballistic missile was incoming. It took…
Read MoreThe First Line of Defense in Cyber Security
Headlines continue to provide us with more information on large data breaches like Yahoo and Equifax, where cyber attackers gained access to personal information through gaps in security software. But…
Read MoreGateKeeper Assistive Technology for Logging In
The best office tech helps you get your work done with efficiency and convenience. But when you’re working with a disability, challenges to that kind of unthinking ease can crop…
Read MoreProtecting Your Organization – Insider Threat Prevention
Most organizations know that they need cyber security to protect from outside threats, but what they don’t account for is the growing number of insider threats. Insider threats come from…
Read MoreForeign Hackers from the East
From the US presidential election to Kaspersky, there is nary a day that goes by that doesn’t contain at least one reference to nefarious cybersecurity acts sponsored by Russia and…
Read MoreOne Hard Lesson From the Breach of Breaches
Spoiler alert: we’re talking about data breaches – Equifax. It seems like once a week there’s a new hacking making headlines. The one at the top of our list lately…
Read MoreMedical Cyber Security with GateKeeper
Medical cyber security automated for doctors and nurses. GateKeeper is a localized wireless tracking solution that allows for constant real-time monitoring of personnel in a pre-determined and well-defined location. Personnel…
Read MoreWhy Enterprises Should Rush to Adopt Multifactor Authentication.
Phishing attacks, social engineering, database breaches, cyber attacks – all terms that have found their way into our daily lives. If the incessant news of the past decade has shown…
Read More