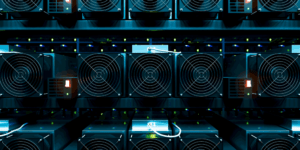
Insider Threats and the Dangers of Crypto Mining to the Enterprise
Although there has been several debates on the advantages and disadvantages of cryptocurrency and the enterprise, one issue with it is cyber security. Dealing with bitcoin or any other cryptocurrency…
The First Line of Defense in Cyber Security
Headlines continue to provide us with more information on large data breaches like Yahoo and Equifax, where cyber attackers gained access to personal information through gaps in security software. But…
How do Cryptocurrency Hardware Wallets Work?
How Does a Cryptocurrency Hardware Wallet Work? The cryptocurrency market continues to grow with many new technological and innovative advancements. The hardware wallet is such an advancement – it stores…
GateKeeper Assistive Technology for Logging In
The best office tech helps you get your work done with efficiency and convenience. But when you’re working with a disability, challenges to that kind of unthinking ease can crop…
Protecting Your Organization – Insider Threat Prevention
Most organizations know that they need cyber security to protect from outside threats, but what they don’t account for is the growing number of insider threats. Insider threats come from…
One Hard Lesson From the Breach of Breaches
Spoiler alert: we’re talking about data breaches – Equifax. It seems like once a week there’s a new hacking making headlines. The one at the top of our list lately…
Medical Cyber Security with GateKeeper
Medical cyber security automated for doctors and nurses. GateKeeper is a localized wireless tracking solution that allows for constant real-time monitoring of personnel in a pre-determined and well-defined location. Personnel…
Why Enterprises Should Rush to Adopt Multifactor Authentication.
Phishing attacks, social engineering, database breaches, cyber attacks – all terms that have found their way into our daily lives. If the incessant news of the past decade has shown…
Continuous and Convenient 2FA
We all use some form of authentication—passwords, passcodes, an ID card—upon entering into a place with restricted access. Whether this place is digital or real-world, authentication systems are typically founded…