What is AES-256 Encryption?
AES-256 Authentication explained.
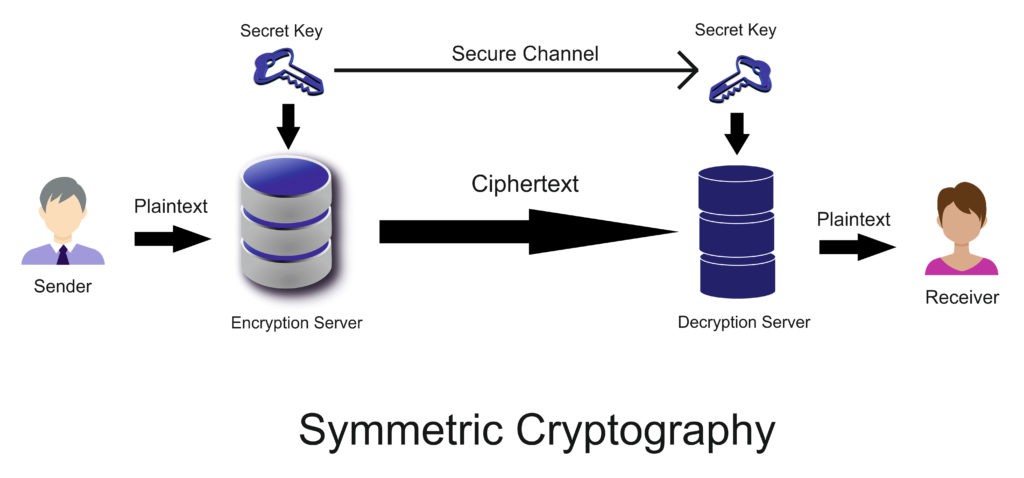
AES-256 is a publicly accessible cipher approved by the U.S. Federal government for protecting secret information. AES (or Advanced Encryption Standard) is referred to as block cipher where the information to be encrypted is categorized into sections called “blocks”. AES-256 has a key length of 256 bits and is considered unbreakable by brute force attacks. The larger the key size means there are more combination possibilities.
In today’s increasingly digital world, cybercriminals are always on the prowl, trying to hack and break the weakest links in an organization’s computer network. Because of this, authentication has become a security fundamental for every firm, be it a local startup or an MNC. AES-256 has become the market standard to protect important data against unauthorized users.
How Difficult is it to Break AES-256?
AES-256 provides the strongest level of encryption as it offers the longest key combination, having 256 bits. That is, a cybercriminal needs to apply 256 different password combinations to guess the right one, which makes it virtually impossible to crack the password. Because of this, the U.S. government uses AES-256 for protecting data concerning national security.
Similarly, AES-256 uses 14 rounds of encryption, compared to 10 rounds of AES-128, and 12 rounds of AES 192. The greater number of rounds makes AES-256 the strongest AES algorithm in practice.
At the same, AES-256 consumes 40% more computer system resources than AES-192, making it most suitable for national-level, high-sensitive security environments where security supersedes speed. AES-256 would take billions of years to crack using a powerful computer to brute force.
Enterprise 2FA with tap and go login plus an integrated password manager. One key for all your passwords. Experience fully automated login and security. For example, faster MFA, auto-OTP, password manager, and worry-free workflow with proximity-based privileged access management for Windows 11, 10, 8, 7, VPNs, websites, and desktop applications including MES, EHR, CAD/RMS, and more. Overall, a massive upgrade to security and efficiency.

